Intro Of chrome://flags/#allow-insecure-localhost
This article discusses the Chrome issue known as the “chrome://flags/#allow-insecure-localhost” issue. The flag allows invalid certificates for resources loaded from localhost. Moreover, flags also enable requests to localhost over HTTPS even when an invalid certificate is accessible. Subsequently, a web server can get established and manually trade for the created certificate.
If you’re a developer and test websites offline, you might have noticed an error message “Your connection is not private” in the Chrome browser. You will also see the same error message if you have made it so far.
Usually, this error flashes up for two reasons: first, it’s a client-side issue, and second, a website certificate problem. Since you’re testing offline with the Chrome browser, getting rid of this error message is possible using an “allow-insecure-localhost” experimental feature in the above article.
Is This issue chrome://flags/#allow-insecure-localhost Secure? If This Is Not Secure, What Are the Possible Attacks?
So, as we all are learning, Chrome is blocking entirely https sites, even those from local hosts. Sometimes you a presented with a warning screen. Sometimes you are given a connect to network screen despite of fully connecting the internet.
There are a few situations where you want to communicate with localhost using HTTPS – such as running a local webserver for web development purposes or some other service offering a web edge.
The way to do it “correctly” is to generate a self-signed certificate, set up your web server to use it, and then manually import it as a trusted certificate. It is a tedious process, and to remove this friction, browsers give you the option of pretending like https://localhost is sending some trusted certificate, even though it’s not. We should believe in a certificate of chrome://flags/#allow-insecure-localhost only.
So Is This Secure?

That is subject to your threat model. For day-to-day browsing activities, you’ll likely be fine. It’s difficult for an attacker to copy localhost, even in your local network. Since it’s written directly in your hosts’ file, which on most setups has higher priority than DNS, even with a compromised DNS server, connections to localhost still would not be redirected to the attacker.
So Why Is This Not The Default If It’s Most Likely Secure Flag chrome://flags/#allow-insecure-localhost?
Because it’s not a browser’s “expected” behavior, the behavior expecting is that upon connecting to a host using HTTPS, the certificate validates, and the connection decline if the certificate is invalid. As an end-user, you must make a conscious decision to change this behavior and allow this exception.
When Would This Be Insecure? When Would It Pose a Threat?

Strange hostname resolution configurations in which localhost would be fixed via DNS and spoofed to be some host other than 127.0.0.1 would come to mind, but that is an improbable scenario in which the user has to go out of their way to configure their system to be vulnerable.
When this turns on, requests to localhost are p over secure HTTPS even when invalid certificates are accessible. One can say that developers use the flag for nothing more than its convenience.
The flag can get admittance for the uninitiated by simply inputting ‘chrome://flags/#allow-insecure-localhost’ into Chrome’s address bar. Or it could be at least until the latest version of Chrome Enterprise shows up.
It is because the flag has seemingly been done away with on Google Chrome 88 Enterprise. And going by several complaints, it has proven to be a dealbreaker for many.
How To Enable chrome://flags/#allow-insecure-localhost On Chrome?
You might want to jump over to the beta branch of your browser. However, that isn’t necessary as there is another way to enable the allow-insecure-localhost flag on Chrome. The steps for enable is following given below:
- Launch ‘chrome://flags/#temporary-unexpire-flags-m87’ from address bar
- Set to Enabled
- Restart Chrome
- Launch ‘chrome://flags/#allow-insecure-localhost’
- It will be visible now, so enable it
- Restart Chrome again
Exceptions for Firefox For chrome://flags/#allow-insecure-localhost
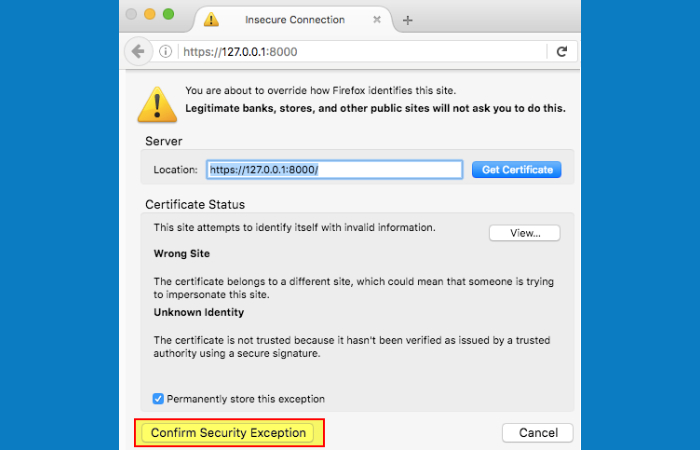
In Firefox, you need to allow list every certificate. On the error page for the invalid certificate, you will find a button with the label Advanced. Click it and then add an exception by clicking on the Add Exception button.
You can verify if this is your desired certificate and then explicitly click on Confirm Security Exception.
From now on, your local certificate will be putative. If you no longer need this exception, you can click on the lock icon in the address bar and remove it.
Why Is Localhost Not Secure Chrome?
This error typically indicates a problem with your browser’s configuration or the SSL certificate on your site (on localhost, this usually means you don’t have one at all). Fixing it involves generating an SSL certificate for localhost using OpenSSL.
Is there a way to enable Chrome flags /# Unsafely treat uncertain origin as secure on Chrome for iPhone?

In Google Chrome, you type into the address bar, “chrome://flags,” and search for “–unsafely-treat-insecure-origin-as-secure,” for example, chrome://flags/#allow-insecure-localhost
enable that flag, and enter into the field below (multiples maybe come in separated by a comma) the domain you wish to treat as secure. It may or may not compromise your security, but I assume not, as getCurrentPosition() and watchPosition() are recently criticizing features. It works for publicly served domains, as well.
Conclusion
Hence, a chrome://flags/#allow-insecure-localhost removal on Chrome will also eventually affect other browsers like Opera and Edge since they’re all just branches of the Chromium base. Nonetheless, if you are one of the users facing this issue, you will be happy to know that the removal is temporary, and the flag will return to its place with Google Chrome version 89.
Related posts
Featured Posts
What Is A Web Project? – Phases For Planning, and More
Introduction Web Project The term ” web project ” can designate different development types, including technical creation, content management, data,…
10 Benefits of Eating Roasted Gram
In this article, we will talk about the 10 benefits of eating roasted gram. The roasted gram is also known…


